It goes without saying that your server has to be safe and secure. Therefore, you will need to know how to secure a Linux server to protect your website. Also, securing Linux, you will need to consider your hosting agent, protect the network with firewalls, and update the web apps you utilize.
The main reason why you would better do it is that your website might be attacked directly. However, the webserver hosting the website might do the same. The website might be threatened by viruses, intrusions, phishing, and hacking attempts. Therefore, your IT department and hosting service need to protect the server from attacks in a proactive way. So you might wonder how to make a Linux server the way hackers will not know your sensitive information.
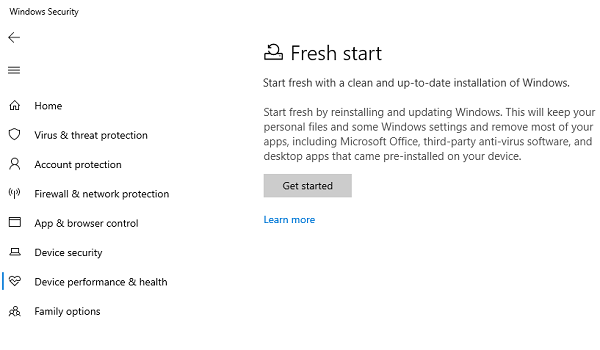
Your selection of Operating System (OS), server, or host agency- Apple, Linux, Microsoft Windows – will tell you what you are supposed to put properly in place to currently meet the best practices on security. Therefore, it is important to configure and review every operation aspect.
To boost the security of your server, you would better take the following six steps. Note that it will be ideal to combine various security measures for excellent results. So, if you wonder, “What are the steps to securing a Linux server?” here are your answers.
1. Use VPN.
If you have a Linux server, you would better download the VeePN to protect you from hacker attacks. For instance, on the VeePN VPN for Linux download page, you will be able to check out the free VPN trial option. If you need more assistance, you might also use VPN apps. Downloading your VPN is the first thing you would do better if you want to know “What are your first three steps when securing a server?”
2. Utilize security tools.
There are security tools (mod security, URL scan) on every server software. The administrators might set up to assist in securing the installation of the webserver. The process of configuring these devices might be with custom web apps and time-consuming. However, they will provide you with peace of mind.
Scanners might run proficiency security checks against network services and open ports to assist in securing your web apps and server. They might check for vulnerable places such as Cross-site scripting, SQL Injection, and web server configuration issues. Some might also automatically audit the shopping carts as well as dynamic web content, check forms, and flag up any problem found.
3. Review the server status.
If you follow a routine and regular monitoring process, you might catch an issue before it shows up. Start with conducting the server status’ review. Check whether there are any issues with its running processes, disk usage, RAM, and CPU, and other metrics because they will often assist in detecting server security problems.
Perfectly, you should store database logs (Oracle, MySQL, Microsoft SQL Server), site access logs, network services logs and check them from time to time. Then, you should investigate the reason for any strange log entries you notice. It will be perfect for keeping scripts always on a separate drive, away from your logs, operating system, and other system files. Once you are done with that, if the hacker tries to access the webroot directory, they will not control your server by utilizing the operating system command.
4. Permissions.
If you wonder, “What steps will you take to secure a server?” consider looking at your permissions. If the account is hacked, the network and file services permissions will limit any potential damage. It will always be a proper practice to schedule regular file system permissions reviews. You should grant the minimal privilege that is required for a particular network service to run. Then, you should restrict what every user or service might do to a minimum. You should disable any case of default account shells that are not normally accessed. Then, you should consider removing your root account to make it possible to login using SSH.
5. Set up the perimeter security with firewalls.
Apps like firewalls and border routers might assist your filter in acknowledging bogus IPs, DDoS filters, malicious traffic, automated attacks, threats, and untrusted networks. The local firewall might monitor the attacks like SSH password guessing and port scans. It may also block any security threat from the attacks. The web app firewall might also filter the web page requests that are incoming. It may also block any that has been generated deliberately to compromise or break your website.
6. Remove all unimportant services.
Common network configurations (RAS, Print Server Service, Remote Registry Services) and default operating system installations are not secure. The ports are rather vulnerable to offend with more services that are running on the operating system. Therefore, it would be better to disable all unimportant services.
It is essential to ensure server security for any business that is operating online. However, it is crucial, especially for those that are permitting network transactions. As for them, this might be a huge problem that you cannot neglect. Increasingly, the network transactions are being protected through the HTTPS and SSL certificates adoption to encrypt communications. To sum up, to harden your Linux server, you will not need to apply a lot of effort. The extra security layers should and can be enabled depending on the way the server is utilized. If you follow all these six tips, they will assist you in securing your web server and keep your resources and information safe.






Add Comment