Law firms handle many files and records every day — letters, emails, pleadings, contracts, and a lot more (check this out). Managing all of these documents can be overwhelming, especially without a standardized system for organizing, securing, and retrieving documents. These are the backbone of any legal enterprise, and being able to handle them well is directly related to your success.
In terms of document management systems, law firms are in a different position. For some enterprises, sharing file drives and email-based communication are two of the best options to improve efficiency as it is simply cost-effective and most convenient. However, this isn’t the option for a typical law firm.
Lawyers are not in any position to disclose any of their client’s information. It is integral to see a reliable way not to jeopardize attorney-client confidentiality, so implementing shared file drives seems impossible. At the end of the day, lawyers must demand higher performance from their IT infrastructure to secure protected documentation and records.
The Reasons Why Are Lawyers Targeted By Cybercriminals
Lawyers are seen as more vulnerable to cybercrimes. Especially most are in remote working environments (link: https://practice.findlaw.com/how-to-start-a-law-firm/law-firm-document-retention-and-destruction-policies.html). Because they lack infrastructure security when working from home, they are considered the easy targets. In addition, we could agree that every lawyer holds a massive amount of valuable documents. These aren’t just personal and private client information but also business documents about finances, transactions, due diligence, mergers and acquisitions, and a lot more sensitive data.
Hackers stand to gain in a variety of ways from such attacks. Some of the most common include selling your information to third parties or holding your personal data to commit identity theft crimes.
However, the next step if you’ve been a cyberattack victim isn’t just the recovery process of data and info. They can also result in compliance violations, not to mention the eye-watering penalties, which can jeopardize your good reputation and all of your efforts to grow your law firm.
This is why you should make some ways to protect your files, especially virtually. Here we’ve listed some of the tips to get secure management.
1. Getting The Right Document Management System
Getting the right management system for your documents or record is essential for organizing, securing, digitizing, approving, and better workflow for your files. It acts much more than cloud storage because effective software, like legal IT support, also features surveillance to monitor the documents 24/7. This helps see the logs in a workforce.
On top of a blanket of security, an effective document management system can help make things easier. You can find documents quicker, and you can organize them on how you want them to be. It is automated, so it advances in mobility, collaboration, and efficiency, compared to manual documentation.
Given that, this can save and reduce the physical storage capacities in your firm, allowing your entire staff to benefit from a more streamlined approach to accessing legal documents.
2. Cybersecurity And Data Protection Awareness
With the implementation of emerging technologies and digital transformations, law firms are undeniably vulnerable to becoming a common target for cybercrimes. Because the legal sector includes data that is directly linked to a large volume of confidential information (politics, public figures, personal information, intellectual property, etc.), criminals view it as an opportunity to exploit breached information for misuse and even financial gain! It can be phishing or malware; they could pose a threat to some legal firms, particularly those that do not place a high priority on their cybersecurity policies.
It is critical to have a cybersecurity program where the employees are trained for cyber awareness in the legal industry. Over the last two years, the cost of cybersecurity threats has increased by 31%, with most serious threats directed at internal employees. With that said, it may be worthwhile to consider implementing a training program that teaches employees how to spot fraudulent email addresses and phishing attacks or even accidental user errors. Upon hiring, training should be a requirement, and it should be utilized periodically thereafter.
3. Use Strong Passwords
Don’t be silly, and stay out of the obvious. For the love of all things cyber, never, ever use the usual—”12345”—please, no. Don’t use sequential numbers or letters on your security passwords because they’re too easy for hackers to guess. Create one-of-a-kind passwords that do not contain any personally identifiable information such as your name or birthdate.
For greater password security, choose something complex and lengthy. Or you can install password management software to keep your passwords strong and impossible for criminals to hack.
4. Access Control And Making Restrictions
There should be different levels of access for every employee. Some of them don’t need to know everything about your transactions or records. When considering whether to grant permission to view specific matters, be deliberate in your decision.
You can keep confidential or sensitive files out of reach and restricted for certain people. In this way, this can help prevent or monitor an event of audit or data breach. Be sure to follow the principle of least privilege to mitigate risks.
5. Plan B For Everything
Some cyberattacks are often unavoidable these days, especially if you don’t know how to deal with a minor attack. Worse— they can quickly escalate into a larger issue.
You must have a plan in place to deal with the aftermath of an attack to respond effectively.
For your first line of defense, it should be your IT team, whether in-house or outsourced.
If ever you’ve been attacked virtually, it is best to be vigilant to contain the damage (read more) and recover as fast as possible—from little to no financial and reputation damage.
Have a professional check your system
Change the sever’s password, as well as your emails and devices
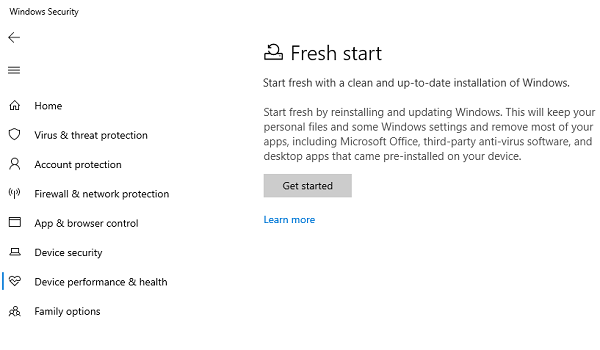
Scan all the servers if there’s running malware or virus
Check the logs
Look for the data that has been breached
Secure your Wi-Fi routers








Add Comment